How VREM aligns with the zero trust maturity model for data
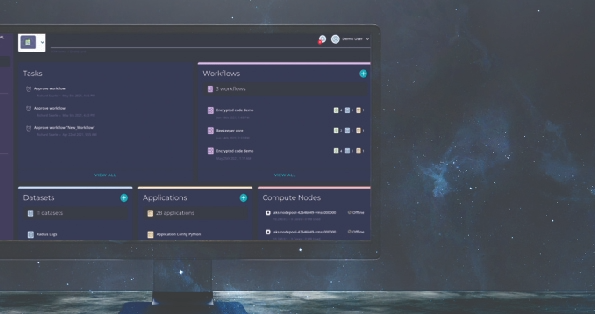
VREM applies a unique, data-centric approach to security. Our innovative data security and privacy platform is based on confidential computing technology to ensure data is securely protected in hybrid and multi-cloud environments This platform serves as a decentralized hub for managing encryption tasks, giving users complete control over data protection.
Through granular access controls, only approved identities (either human or machine) can access the encryption/decryption keys. Administrative safeguards, such as "Quorum Approval Policies," protect the keys from mistakes or malicious actions.These VREM platforms offer the following solutions:
Data Security Manager (DSM)
provides modern, scalable, and cloud-friendly solutions such as enterprise key management with integrated HSMs, secrets management, and tokenization. Powered by Confidential Computing technology, it supports standard cryptographic APIs such as PKCS #11, JCE, and CAPI/CNG alongside a powerful and comprehensive REST API for application developers and DevOps teams, enabling seamless integration with both third-party applications and in-house applications.

Enclave Development Platform (EDP)
is an open-source toolset for developing your own confidential computing applications running inside secure enclaves using the security-focused Rust programming language.
Confidential Computing Manage
enables you to convert your existing containerized applications to run inside a secure enclave and to orchestrate and manage confidential computing applications across your on-premises or private/public cloud infrastructure.
Data inventory management
Zero trust requirement
| ZTMM requirement | What it entails | Required capabilities |
|---|---|---|
| Data inventory management | Continuously keep track of all relevant data within the organization and use effective strategies to prevent data loss by blocking suspicious data transfers. |
|